Overview
On August 3, 2025, threat intelligence firm GreyNoise detected an unprecedented surge in brute-force login attempts targeting Fortinet SSL VPN appliances, with over 780 unique IP addresses involved in a single day.
Historically, 80% of similar brute-force surges are followed by public vulnerability disclosures—often within six weeks. If this trend continues, defenders should prepare for the possibility of a zero-day or new CVE affecting FortiOS or FortiManager before late September.
Incident Timeline
1. Initial Spike – August 3, 2025
- FortiOS SSL VPN profiles targeted.
- Single distinct TCP signature observed, suggesting a specific brute-force tool.
- Over 780 unique IPs participated—breaking prior records.
2. Evolution Phase – August 5, 2025
- Attack methodology pivoted.
- New TCP signature with distinct client fingerprints detected—possibly indicating new tooling or updated modules.
- Expanded targeting from FortiOS to include FortiManager (FGFM) services.
Geographic Hotspots
In the past 90 days, Hong Kong and Brazil have been the most targeted regions. While many attacks are proxied, these hotspots may align with high-value Fortinet deployments.
Attack Waves Identified
| Wave | Description | Notes |
|---|---|---|
| One | Long-term campaign | Same TCP signature for weeks/months; persistent ops |
| Two | Coordinated burst | New TCP signature; simultaneous VPN and FGFM focus |
- Wave One: Stable TCP signature, likely from an established infrastructure.
- Wave Two: Began August 5 with retooled methods, expanded targeting—likely the same operators.
Infrastructure Notes
- Residential Proxy Presence: Observed FortiGate device at residential ISP (Pilot Fiber Inc.), possibly used as a proxy, compromised home device, or test environment.
- Toolset Reuse: Several IPs active on August 3 linked to known malicious infrastructure—suggesting shared resources.
Risk Correlation
GreyNoise data indicates brute-force spikes against Fortinet often precede CVEs—with 80% resulting in a disclosure within six weeks. August–September 2025 is therefore a critical monitoring period.
Why This Matters
Fortinet SSL VPN and FortiManager are key gateways for corporate networks, often exposed to the public internet. These devices are prime targets for:
- Initial Access Brokers (IABs)
- Ransomware affiliates
Brute-force attacks may be credential harvesting in preparation for future exploitation—especially if a new vulnerability emerges.
Recommendations for Defenders
- Restrict VPN Access: Block risky regions.
- Rate Limiting: Apply authentication rate limits.
- Enforce MFA: Require for all VPN and FortiManager accounts.
- Patch Now: Apply latest security updates.
- Monitor Fortinet Bulletins: Watch advisories for the next 6 weeks.
- Audit Logs: Check for unusual login failures or geolocation anomalies.
- Block IOCs: Add to firewall, SIEM, and threat intel feeds.
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
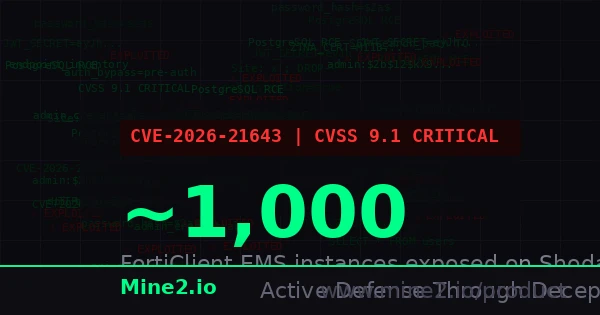
FortiClient EMS Under Fire: CVE-2026-21643 Turns Endpoint Management Into an Attacker's Credential Goldmine
WinRAR Zero-Day Vulnerability CVE-2025-8088 Exploited by RomCom to Deliver Backdoor Malware
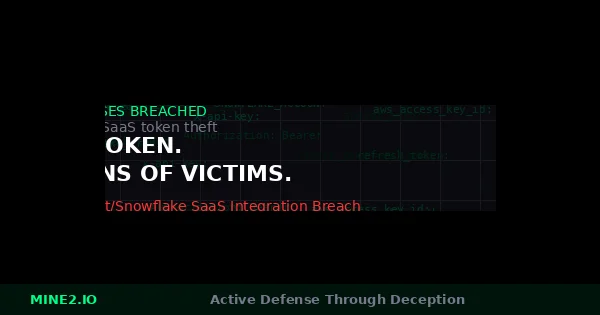
One Token, Dozens of Victims: How the Anodot SaaS Integration Breach Rewrites the Third-Party Risk Playbook
Need Security Help?
Protect your organization with MINE2's cyber deception platform.