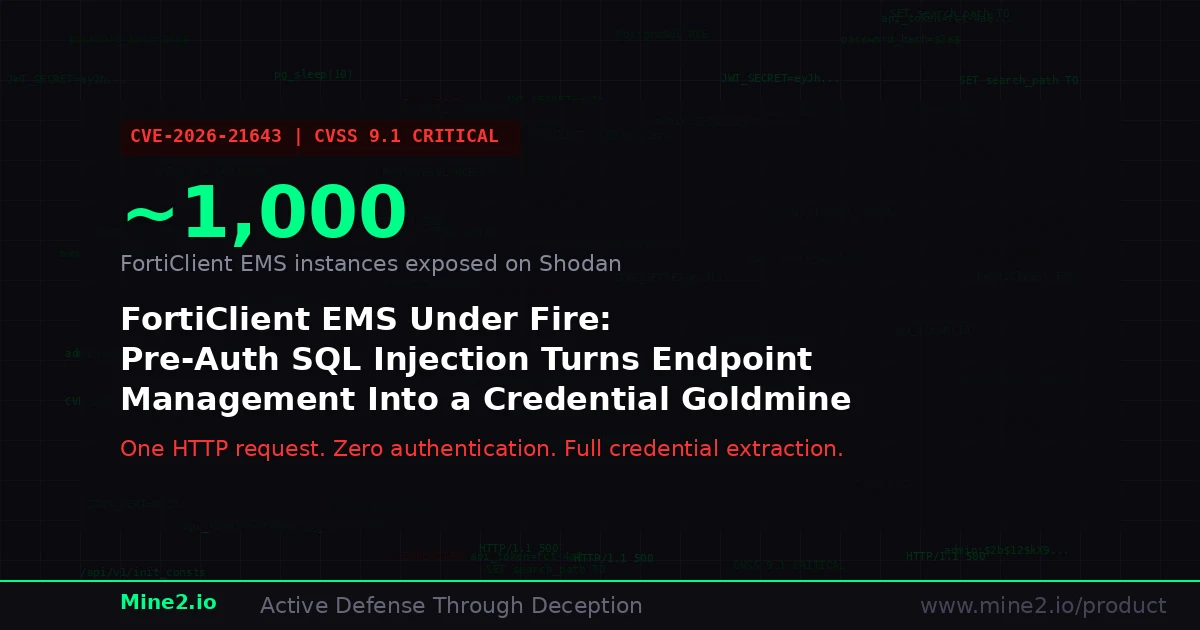
Nearly one thousand FortiClient Endpoint Management Server instances sit exposed on the public internet right now. Since March 26, 2026, threat actors have been exploiting a critical SQL injection vulnerability — CVE-2026-21643, rated CVSS 9.1 — that requires no credentials, no user interaction, and exactly one HTTP request to turn every one of those servers into an open credential vault. The flaw hands attackers admin password hashes, JWT signing secrets, ZTNA certificates, complete endpoint inventories, and in some deployments, direct remote code execution through PostgreSQL superuser privileges.
This is not a theoretical risk. Bishop Fox researchers demonstrated that a crafted Site header — the HTTP field that identifies which tenant a request belongs to — bypasses all authentication because the injection point sits in the SiteMiddleware layer, which executes before AuthMiddleware even loads. Fortinet's own security researcher, Gwendal Guégniaud, identified the flaw internally, and the patch to version 7.4.5 has been available since late 2025. Yet the exploitation wave that began four days before public confirmation on March 30, 2026, suggests that hundreds of organizations still run the vulnerable 7.4.4 release with multi-tenant mode enabled.
For security teams, the uncomfortable truth is that patching the server closes the door but does nothing about credentials that were already stolen. When an attacker walks away with every admin hash, every JWT secret, and every endpoint certificate in your EMS database, the compromise does not end with a version upgrade. It begins.
Why Endpoint Management Servers Are High-Value Targets
Endpoint management platforms occupy a uniquely privileged position in enterprise architecture. FortiClient EMS does not merely push antivirus signatures — it controls security policy enforcement, VPN configurations, zero-trust network access certificates, and vulnerability scanning schedules for every managed device. Compromising the EMS gives an attacker the kind of visibility and control that would normally require weeks of internal reconnaissance.
The data exposed through CVE-2026-21643 reads like an adversary's wish list. Admin credentials and API tokens provide immediate authenticated access to the management console. The endpoint inventory — hostnames, IP addresses, operating system versions, serial numbers, installed software — is a complete network map. ZTNA certificates allow an attacker to impersonate legitimate endpoints and bypass zero-trust policies entirely. Security policy configurations reveal which defenses are active, which endpoints are exempt from scanning, and where the gaps exist.
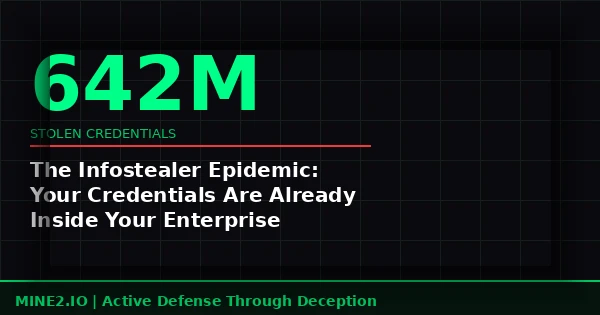
This is precisely why credential theft from management platforms has become the dominant initial-access vector in 2026. According to CYFIRMA research, modern ransomware operations increasingly rely on stolen credentials rather than exploit-driven intrusions, using data harvested from management consoles and infostealers to bypass perimeter defenses and enable rapid lateral movement through legitimate authentication channels. In January 2026 alone, approximately 149 million stolen credentials were exposed through infostealer infections — and a single compromised EMS instance can add thousands more high-privilege credentials to that pool.
The Anatomy of a FortiClient EMS Attack Chain
Understanding how CVE-2026-21643 is exploited reveals why traditional security tools struggle to detect the downstream activity.
The attack begins with a simple HTTP request to the publicly accessible /api/v1/init_consts endpoint. This endpoint requires no authentication and has no rate limiting. The attacker injects SQL through the Site header using a straightforward string escape.
The vulnerable code uses format-string interpolation instead of parameterized queries, meaning the tenant name from the HTTP header is concatenated directly into the SQL statement. By injecting a single quote and semicolon, the attacker breaks out of the intended query and executes arbitrary SQL against the backing PostgreSQL database.
The /init_consts endpoint is particularly dangerous because PostgreSQL errors are returned in HTTP 500 responses. Attackers use error-based extraction — wrapping queries in type-cast operations that force the database to include query results in error messages. This technique extracts data without needing any visible output field, making detection through web application firewalls extremely difficult.
In laboratory testing, Bishop Fox researchers confirmed that baseline response times of 77 milliseconds jumped to over 10 seconds when a pg_sleep(10) injection was introduced — clean timing confirmation that the injection is reliable and consistent.
Once inside the database, the attacker follows a predictable sequence. First, they extract admin password hashes and JWT signing secrets. Second, they pull the complete endpoint inventory to map the internal network. Third, they harvest ZTNA certificates to forge endpoint identities. In VM-based deployments where PostgreSQL runs with superuser privileges, the attacker can escalate to operating system command execution through PostgreSQL's COPY ... TO/FROM PROGRAM functionality — achieving full remote code execution on the server itself.
The critical gap appears in what happens next. The attacker now possesses legitimate credentials, valid certificates, and a detailed network map. Every subsequent action — logging into the EMS console, pushing modified security policies, connecting to endpoints using stolen ZTNA certificates — uses legitimate authentication channels. Firewalls see authorized traffic. SIEM rules see successful logins. EDR agents see management operations from a trusted source.
Why Traditional Security Controls Miss Post-Exploitation Activity
The fundamental challenge with CVE-2026-21643 is not the injection itself — SQL injection has well-understood detection signatures. The real problem is what happens after credential extraction, because every tool in the traditional security stack is optimized to detect anomalous or unauthorized behavior, not legitimate-looking access using stolen credentials.
Firewalls and network segmentation cannot distinguish between an administrator logging in from a VPN and an attacker using that administrator's stolen credentials from the same network path. Security Information and Event Management systems generate alerts on failed logins, impossible travel, and known-bad IP addresses — but an attacker who possesses the correct password hash, forges a valid JWT token, and connects from a nearby IP range produces no anomalous signals.
Endpoint Detection and Response tools monitor for suspicious process behavior, malware signatures, and exploitation techniques. When the attacker uses stolen ZTNA certificates to connect to managed endpoints through the legitimate FortiClient channel, the EDR agent sees exactly what it expects to see: authorized management traffic from a trusted source.
Even Privileged Access Management solutions assume that the credentials stored in their vaults are the only copies that exist. CVE-2026-21643 creates a parallel set of credentials outside the PAM system's awareness, rendering session recording, just-in-time access, and credential rotation meaningless until the stolen credentials are specifically revoked.
This detection gap is not unique to FortiClient EMS. It exists whenever attackers compromise any management platform — BeyondTrust, CyberArk, Microsoft SCCM, or any system that stores credentials and controls endpoint configurations. The pattern is consistent: steal credentials from the management layer, then move laterally using those credentials through channels that every other security tool considers trusted.
How Cyber Deception Catches What Other Controls Cannot
Deception technology solves the post-exploitation detection problem by fundamentally changing the attacker's environment. Instead of trying to distinguish legitimate credential use from stolen credential use — a problem that is mathematically intractable for signature-based tools — deception plants fake credentials that no legitimate user or system would ever touch. Any interaction with these decoy credentials is, by definition, malicious.
Credential Mines are fake admin accounts, API tokens, and password hashes planted directly in the environments that attackers target. In the context of CVE-2026-21643, Credential Mines placed in the FortiClient EMS database would appear indistinguishable from real admin accounts. When an attacker extracts the database contents, they harvest the mines along with legitimate credentials. The moment any of those fake credentials are used to authenticate — whether to the EMS console, a managed endpoint, or any other system — Mine2 generates a high-fidelity alert with zero false positives.
This detection is impossible for the attacker to avoid. They cannot distinguish Credential Mines from real credentials without testing each one, and every test against a monitored system triggers the alert. Unlike signatures or behavioral baselines, there is no tuning period, no noise floor, and no legitimate use case that could generate a false positive.
AD Mines extend this principle across Active Directory. Fake service accounts, domain admin credentials, and Kerberos SPNs planted in AD ensure that Kerberoasting attacks — the technique most commonly used to escalate privileges after initial credential theft — immediately trigger detection. When an attacker who compromised EMS credentials pivots to Kerberoasting domain accounts, AD Mines ensure that at least some of the returned tickets correspond to monitored decoys.
MineField decoy services detect the reconnaissance phase that follows credential theft. After extracting the endpoint inventory from FortiClient EMS, an attacker will scan the listed IP addresses and ports to identify high-value targets. MineField deploys decoy TCP services across the network that respond to connection attempts and port scans. Any interaction with these services — which no legitimate user or application would contact — generates an immediate alert with full attribution, catching the attacker during lateral movement before they reach any real asset.
Cloud Mines address the increasingly common scenario where FortiClient EMS manages endpoints that access cloud resources. Fake AWS access keys, Azure service principal credentials, and GCP service account keys planted in locations that attackers check — environment variables, configuration files, and credential stores — detect cloud pivot attempts. When an attacker who stole EMS credentials attempts to leverage endpoint access for cloud resource enumeration, Cloud Mines fire on the first API call.
Meeting Compliance Requirements Through Deception-Based Detection
The breach notification timelines imposed by modern regulations make deception technology not merely a security advantage but a compliance necessity. When CVE-2026-21643 is exploited, the clock starts ticking immediately — but organizations cannot notify what they cannot detect.
CERT-In 6-Hour Reporting Mandate: India's CERT-In requires incident reporting within six hours of detection. Deception-based alerts — which fire within seconds of credential reuse — provide the earliest possible detection, giving security teams the maximum available window for investigation, containment, and reporting. Without deception, organizations relying solely on log-based detection may not identify credential theft from EMS for days or weeks.
India DPDP Act (2023): The Digital Personal Data Protection Act requires organizations to notify the Data Protection Board and affected individuals of any breach involving personal data. FortiClient EMS stores endpoint inventory data that may include employee device information, network locations, and software configurations — all of which qualify as personal data. Deception technology provides the audit trail necessary to demonstrate when a breach was detected and what containment actions were taken.
GDPR Articles 33 and 34: The 72-hour breach notification requirement under GDPR demands that organizations detect breaches rapidly and document the scope of data exposure. Credential Mines create a forensic trail that shows exactly when stolen credentials were first used, from which IP address, and against which systems — providing the evidence required for supervisory authority notification.
PCI-DSS Requirement 11: PCI-DSS requires organizations to test security systems and processes regularly, including implementing change-detection mechanisms and performing quarterly vulnerability scans. MineField decoy services serve as continuous monitoring controls that satisfy Requirement 11.5's file integrity monitoring provisions while simultaneously providing real-time intrusion detection.
RBI and SEBI Cybersecurity Frameworks: India's financial regulators mandate comprehensive cyber resilience frameworks that include continuous monitoring and rapid incident detection. The Reserve Bank of India's cybersecurity guidelines specifically emphasize the need for proactive threat detection capabilities. Deception technology's zero-false-positive alerting model directly addresses these requirements while reducing alert fatigue that degrades SOC effectiveness.
HIPAA Security Rule: Healthcare organizations using FortiClient EMS to manage clinical endpoints must detect unauthorized access to systems containing electronic protected health information (ePHI). The Security Rule's requirement for audit controls (§164.312(b)) and access controls (§164.312(a)) is directly supported by Credential Mines, which create an irrefutable audit trail of unauthorized credential use.
A Practical Playbook for Defending Against EMS Credential Theft
Organizations that run FortiClient EMS — or any endpoint management platform — should implement the following layered defense strategy:
Immediate Actions (0-24 hours)
First, verify your FortiClient EMS version. If running 7.4.4 with multi-tenant mode enabled, upgrade to 7.4.5 immediately. Check Shodan and Censys for your organization's exposure. Remove EMS administrative interfaces from public internet access.
Second, rotate all credentials stored in the EMS database. This includes admin accounts, API tokens, JWT signing secrets, and ZTNA certificates. Assume that if your EMS was exposed, the database has been read.
Third, review authentication logs for the EMS /api/v1/init_consts endpoint. Look for unusual Site header values, HTTP 500 responses, and requests from unexpected source IPs. These are indicators of exploitation attempts.
Short-Term Hardening (1-7 days)
Deploy Credential Mines in your endpoint management database. Plant fake admin accounts with realistic naming conventions that will be harvested alongside real credentials during any future extraction attempt. Configure monitoring to alert on any authentication attempt using these decoy credentials.
Deploy MineField decoy services on IP addresses listed in your endpoint inventory. When an attacker who stole the inventory begins scanning those addresses, the decoy services will detect the reconnaissance before any real endpoint is contacted.
Implement network segmentation that isolates the EMS administrative interface from general network access. Require multi-factor authentication for all EMS console logins and API access.
Ongoing Defense (7-30 days)
Deploy AD Mines across your Active Directory environment. Plant fake service accounts and admin credentials that mirror the naming patterns used by your FortiClient EMS service accounts. This ensures that credential-based lateral movement from EMS compromise triggers detection at the directory level.
Deploy Cloud Mines in endpoint configurations. Plant fake cloud provider credentials in the same locations where legitimate credentials are stored on managed endpoints. When an attacker pivots from endpoint compromise to cloud enumeration, these mines fire immediately.
Establish a deception-first detection philosophy. Every management platform in your environment — not just FortiClient EMS — should be surrounded by Credential Mines that detect when stored credentials are extracted and reused. This includes PAM solutions, configuration management tools, remote access platforms, and identity providers.
The Bottom Line
CVE-2026-21643 is a stark reminder that endpoint management servers are not just IT infrastructure — they are credential vaults, network maps, and security policy engines rolled into a single target. Patching closes the vulnerability, but it does not address the credentials that were already stolen during the exploitation window.
Traditional security controls were not designed to detect legitimate-looking access using stolen credentials. Deception technology — specifically Credential Mines, AD Mines, MineField, and Cloud Mines — is the only approach that detects post-exploitation activity with zero false positives by planting fake credentials that no legitimate process would ever use.
When the next management platform vulnerability drops — and it will — the organizations that survive will be those that assumed their credentials were already compromised and deployed mines to catch attackers the moment they try to use them.
Discover how Mine2's deception platform can protect your organization from credential theft and lateral movement. Explore Mine2 →
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
React2Shell CVE-2025-55182: 766 Next.js Hosts Breached in Automated Credential-Theft Wave
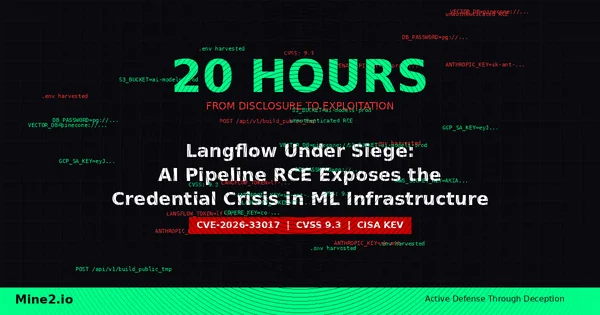
Langflow Under Siege: AI Pipeline RCE Exploited in 20 Hours Exposes the Hidden Credential Crisis in ML Infrastructure
The Infostealer Epidemic: 642 Million Stolen Credentials Are Already Inside Your Enterprise
Need Security Help?
Protect your organization with MINE2's cyber deception platform.