Urgent: CVE-2025-53786 – A Critical Hybrid Exchange Vulnerability That Could Lead to Total Domain Compromise
On August 6, 2025, Microsoft disclosed a critical security vulnerability affecting organizations running Hybrid Exchange Server environments. Designated as CVE-2025-53786, this vulnerability is an Elevation of Privilege (EoP) flaw with a high CVSS score of 8.0. It poses a severe risk of total domain compromise, putting both on-premises and cloud-hosted infrastructure at serious risk.
If left unpatched, this flaw can be exploited by malicious actors to gain undetected access to both on-premises and cloud environments, ultimately leading to a full compromise of your domain. Immediate action is required to safeguard your organization's infrastructure.
🔍 How Does CVE-2025-53786 Work?
The vulnerability primarily affects setups where on-premises Exchange servers are integrated with Exchange Online in a hybrid configuration.
The root cause lies in improper authentication handling (CWE-287), specifically insecure sharing of service principals between the on-premises Exchange servers and Exchange Online.
Attack chain overview:
- Admin-level access is required to the on-premises Exchange server.
- Once gained, attackers manipulate shared service principal credentials.
- They can then forge tokens that are accepted by Exchange Online.
- These tokens allow impersonation of Exchange Online services.
- Attackers gain undetected access to sensitive cloud-hosted mailboxes and services, bypassing Microsoft 365 audit logs.
- Stealthy persistence is maintained, enabling attackers to remain hidden for hours before detection.
⚠️ Affected Versions
The following versions of Exchange Server are impacted:
- Exchange Server 2016 CU23
- Exchange Server 2019 CU14
- Exchange Server 2019 CU15
- Exchange Server Subscription Edition (RTM)
🛠 Immediate Mitigation Steps
Microsoft has released security guidance and patches that must be applied immediately.
1. Apply the Latest Security Updates
- Install the April 2025 Hotfix Updates or later Cumulative Updates for all affected servers.
2. Switch to the Dedicated Exchange Hybrid App
- Replace the legacy shared service principal with Microsoft’s dedicated hybrid authentication model.
3. Reset Cloud Credentials
- Use Microsoft’s Service Principal Clean-Up Mode to reset keyCredentials and secure the environment.
4. Verify Configuration Compliance
- Run the Microsoft Exchange Health Checker to confirm your hybrid environment is secure and compliant.
5. Secure Legacy Servers
- Disconnect unsupported or internet-facing Exchange/SharePoint servers from public access immediately.
📢 CISA's Emergency Directive
In response to this vulnerability, the Cybersecurity and Infrastructure Security Agency (CISA) issued an emergency directive for U.S. federal agencies.
Agencies must patch and reconfigure their affected hybrid Exchange environments by:
📅 August 11, 2025, 9:00 AM EDT
While private organizations are not bound by this deadline, the risk remains equally severe. Immediate action is strongly advised.
✅ Key Takeaways
- Severity: High (CVSS 8.0)
- Risk: Potential for total domain compromise across on-premises and cloud environments
- Exploitation Likelihood: Highly likely, even without confirmed active exploitation
- Action: Patch immediately, modernize hybrid authentication, and conduct thorough access audits
🔒 The Bottom Line
If your organization is running a hybrid Exchange deployment, CVE-2025-53786 should be treated as a critical emergency.
➡️ Apply Microsoft’s patches without delay
➡️ Follow configuration guidance to strengthen hybrid authentication
➡️ Review your authentication setup now — before attackers exploit this flaw
Time is of the essence. Don’t wait for an attack to compromise your domain. Act today to secure your infrastructure.
🛡 MINE2's Perspective
This vulnerability highlights the importance of proactive threat detection in hybrid environments. Traditional security measures often fail to detect sophisticated authentication bypass attacks like this one.
MINE2’s cyber deception platform can help organizations:
- Detect unauthorized access attempts in hybrid environments
- Monitor service principal abuse through honeytokens
- Identify lateral movement between on-premises and cloud systems
- Generate high-fidelity alerts when attackers interact with decoy credentials
👉 Learn more about protecting hybrid environments with MINE2's deception technology.
📚 Sources
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
BitUnlocker: A New Threat to BitLocker Security via Windows Recovery Environment
One Token, Dozens of Victims: How the Anodot SaaS Integration Breach Rewrites the Third-Party Risk Playbook
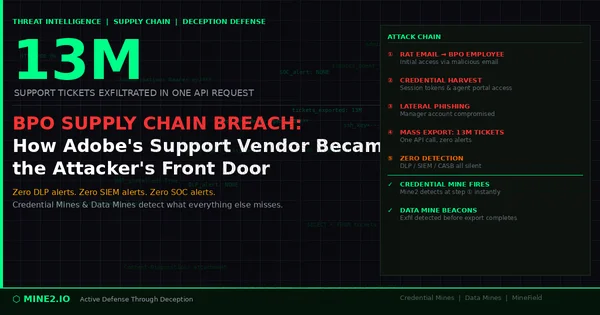
13 Million Tickets, One Request: How the Adobe BPO Breach Exposes the Third-Party Credential Blind Spot
Need Security Help?
Protect your organization with MINE2's cyber deception platform.