WinRAR Zero-Day Vulnerability CVE-2025-8088 Exploited by RomCom to Deliver Backdoor Malware
On August 11, 2025, security researchers from ESET disclosed a critical zero-day vulnerability in the widely-used WinRAR file archiving tool. This flaw, designated CVE-2025-8088, has been actively exploited by the Russia-aligned cyber-espionage group RomCom (also known as Storm-0978, Tropical Scorpius, or UNC2596) in targeted spear-phishing campaigns.
About the Vulnerability
CVE-2025-8088 is a high-severity (CVSS score 8.4) path traversal flaw found in the Windows versions of WinRAR and its components—including UnRAR.dll and the portable UnRAR source code.
The vulnerability leverages alternate data streams (ADSes) to manipulate file extraction paths during archive unpacking. This allows attackers to place arbitrary files, such as executables or LNK shortcuts, into sensitive system folders like Windows Startup directories, enabling automatic execution at login or reboot.
Affected Versions and Patch
- Affected: All Windows releases of WinRAR up to and including version 7.12
- Fixed: WinRAR version 7.13, released on July 30, 2025
- Critical Note: As WinRAR lacks an automatic update mechanism, users must manually download and install the fixed version
Attack Campaign and Timeline
Between July 18 and 21, 2025, RomCom used spear-phishing emails disguised as job applications containing malicious RAR attachments that exploited this flaw. The crafted archives embedded hidden ADS data with crafted paths that forced WinRAR to extract malicious backdoor payloads into sensitive folders allowing persistent system compromise.
Deployed Backdoors
The planted backdoors included variants such as:
- Mythic Agent
- SnipBot
- RustyClaw
- MeltingClaw
These supported remote command execution, credential theft, and further payload delivery. The targeted sectors spanned finance, defense, logistics, and manufacturing across Europe and Canada.
Secondary Exploitation
Shortly after RomCom's exploitation, another threat actor known as Paper Werewolf (aka GOFFEE) was observed leveraging CVE-2025-8088, primarily targeting Russian organizations. The exploit is believed to have been sold for approximately $80,000 on cybercriminal forums.
How the Exploit Works
-
A user receives a spear-phishing email with a booby-trapped RAR archive posing as a resume or job-related document
-
WinRAR extracts files normally but also processes hidden ADS entries specifying relative paths like
....that traverse outside the chosen extraction folder -
This causes malicious executables and LNK files to be placed in critical folders such as the Startup directory
-
The malicious LNK files trigger execution of the RomCom backdoor at system startup or user login
-
The backdoors enable remote control, data theft, and further malicious activities
Recommendations and Mitigations
Immediate Actions
- Immediately update WinRAR and all related components to version 7.13 or later to patch the vulnerability
- Block or quarantine RAR/ZIP attachments from unknown or untrusted sources at email gateways
- Detonate compressed files in sandbox environments before delivery to end users
Additional Security Measures
- Restrict write permissions to Startup folders and other sensitive directories to trusted processes only
- Employ application allow-listing to prevent unauthorized executables from launching
- Conduct user training on the dangers of unsolicited attachments, even if seemingly job-related
- Monitor and detect indicators of compromise (IOCs) associated with RomCom and the exploit's behavioral patterns
IOCs Available
VirusTotal Collection with relevant indicators of compromise.
MINE2's Perspective
This zero-day exploit demonstrates how trusted software can become attack vectors. Traditional security measures often struggle with these sophisticated techniques:
How MINE2 Can Help:
- Email deception that can detect and analyze suspicious attachments before they reach users
- File system monitoring through strategically placed honeypots in startup directories
- Behavioral analysis that detects unusual file extraction patterns
- Lateral movement detection when backdoors attempt to spread through networks
The ability to detect malicious activity even after initial compromise is crucial when dealing with sophisticated APT groups like RomCom.
Discover how deception technology can protect against advanced threats.
Why This Matters
This zero-day exploit highlights the risk posed by vulnerabilities in widely trusted utilities like WinRAR that many organizations use daily. The ability to bypass target extraction paths and implant persistent malware via spear-phishing emails is a potent attack vector.
Given RomCom's history of leveraging zero-days for espionage, the targeted industries, and the stealthy nature of the backdoors, rapid patching and layered defensive measures are critical.
Key Takeaways
- What: WinRAR zero-day vulnerability CVE-2025-8088 exploited via ADS path traversal to plant malware
- Who: Russia-aligned group RomCom (and later Paper Werewolf) targeting finance, defense, logistics, and manufacturing
- Impact: Persistent backdoors allowing remote code execution, data theft, and ongoing control
- Fix: Update to WinRAR 7.13 immediately and implement strict attachment and execution policies
- Importance: Attack exploits trusted software, underscores need for vigilance and multi-layered defense
Summary
By promptly applying patches and enhancing security controls, organizations can defend against this sophisticated zero-day attack and strengthen resilience against emerging supply chain-focused threats.
The WinRAR exploit serves as a stark reminder that even trusted, widely-used software can become vectors for sophisticated attacks. Organizations must maintain comprehensive security strategies that include rapid patching, user education, and advanced threat detection capabilities.
Stay protected against evolving threats with MINE2's comprehensive cybersecurity intelligence and deception technology.
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
Fortinet SSL VPN and FortiManager Under Coordinated Brute-Force Campaign: August 2025 Threat Analysis
One Token, Dozens of Victims: How the Anodot SaaS Integration Breach Rewrites the Third-Party Risk Playbook
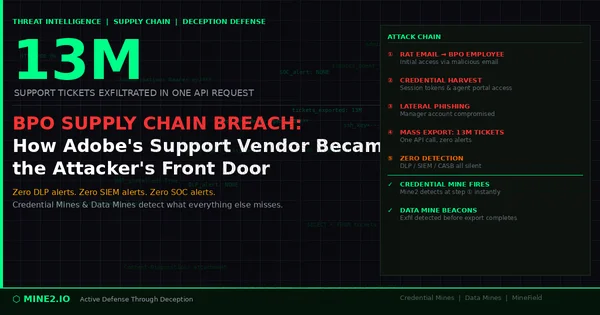
13 Million Tickets, One Request: How the Adobe BPO Breach Exposes the Third-Party Credential Blind Spot
Need Security Help?
Protect your organization with MINE2's cyber deception platform.