BitUnlocker: A New Threat to BitLocker Security via Windows Recovery Environment
On August 11, 2025, Microsoft's Offensive Research & Security Engineering (MORSE) team revealed a series of critical vulnerabilities collectively termed "BitUnlocker" that expose a new physical-attack risk to BitLocker encryption. These vulnerabilities affect multiple Windows platforms, including Windows 10, Windows 11, and Windows Server versions 2016 through 2025.
Understanding BitUnlocker
BitUnlocker refers to four zero-day security flaws found in the Windows Recovery Environment (WinRE). These flaws allow an attacker with physical access to a device to bypass BitLocker encryption entirely, granting unauthorized access to encrypted drives without requiring authentication.
The Four Key Vulnerabilities
Each of these four vulnerabilities scores a medium severity rating (CVSS 3.1 base score of 6.8) and exploits weak validation and trust assumptions inherent in WinRE components:
CVE-2025-48800
Alters Boot.sdi offset pointers to load a malicious recovery image disguised as legitimate.
CVE-2025-48003
Abuses parsing weaknesses in ReAgent.xml to schedule and execute malicious actions that can achieve SYSTEM-level privileges.
CVE-2025-48804
Takes advantage of trust validation flaws in SetupPlatform.exe to provide persistent elevated command access through keyboard shortcuts.
CVE-2025-48818
Manipulates Boot Configuration Data (BCD) to reroute WinRE processes such as the Push Button Reset, causing the system to decrypt BitLocker-protected volumes without verification.
Root Cause and Attack Process
These vulnerabilities arise because WinRE processes external files (configuration files, recovery images, etc.) that are unprotected and lack integrity verification. An attacker can:
- Gain physical access to the machine
- Modify unencrypted recovery partition files such as Boot.sdi, ReAgent.xml, or BCD
- Force the system to boot into WinRE, which then parses the compromised files
- Execute commands or load malicious recovery images with system-level privileges
- Bypass BitLocker encryption, allowing unauthorized decryption of protected volumes
Why This Matters
BitLocker is widely relied upon by both enterprises and individuals to secure data at rest through disk encryption. The discovered flaws undermine the trusted recovery path by allowing attackers to exploit weaknesses in physical security and trust assumptions of the recovery environment.
This elevates the risk of unauthorized data access when an attacker has physical possession of the device.
Mitigation and Patch Guidance
Microsoft addressed these vulnerabilities in the July 2025 Patch Tuesday updates. Users and administrators should:
Immediate Actions
- Apply the July 2025 security patches immediately, which cover all four CVEs
- Enable TPM with PIN pre-boot authentication to enforce two-factor protection binding user input with hardware
- Utilize mitigation tools like REVISE to prevent downgrades or loading of compromised recovery images
- Secure recovery partitions by restricting write access to prevent unauthorized tampering of recovery files
Additional Security Measures
- Implement physical security controls to prevent unauthorized device access
- Monitor for signs of physical tampering on critical systems
- Deploy device encryption policies that require multiple authentication factors
- Regular security audits of recovery environment configurations
MINE2's Perspective
BitUnlocker demonstrates the evolving nature of physical attack vectors against encrypted systems. While BitLocker provides strong encryption, these vulnerabilities highlight the importance of defense in depth:
How MINE2 Can Help:
- Physical security monitoring through honeypot systems that detect unauthorized access
- Behavioral analysis to identify unusual boot sequences or recovery operations
- Credential deception that can alert when attackers attempt to access sensitive data
- Network monitoring to detect data exfiltration after successful BitLocker bypass
Learn more about comprehensive security strategies with MINE2's platform.
Additional Context
The July 2025 Microsoft security update bundle included patches for over 130 vulnerabilities, including critical issues such as a wormable remote code execution vulnerability in NEGOEX and a zero-day information leak in SQL Server.
Despite the BitUnlocker flaws having a medium severity rating, their impact on physical security and the ability to bypass BitLocker makes them a significant concern demanding prompt attention.
Key Takeaways
- What: Four zero-day vulnerabilities in WinRE (BitUnlocker) enable bypass of BitLocker encryption with physical device access
- Impact: Unauthorized decryption of BitLocker volumes without any user authentication
- Fix: Deploy July 2025 patches immediately, activate TPM with PIN, and tighten recovery partition security controls
- Importance: Physical security remains a critical component of overall cybersecurity strategy
Summary
By understanding and addressing these vulnerabilities swiftly, organizations can reinforce their endpoint security against emerging physical-attack vectors that threaten BitLocker's trusted encryption model. The BitUnlocker vulnerabilities serve as a reminder that comprehensive security requires protection against both network and physical attack vectors.
Organizations should prioritize immediate patching, enhanced physical security controls, and multi-factor authentication to maintain the integrity of their encrypted systems.
Stay informed about the latest cybersecurity threats and vulnerabilities by following MINE2's threat intelligence updates.
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
Urgent: CVE-2025-53786 – A Critical Hybrid Exchange Vulnerability That Could Lead to Total Domain Compromise
One Token, Dozens of Victims: How the Anodot SaaS Integration Breach Rewrites the Third-Party Risk Playbook
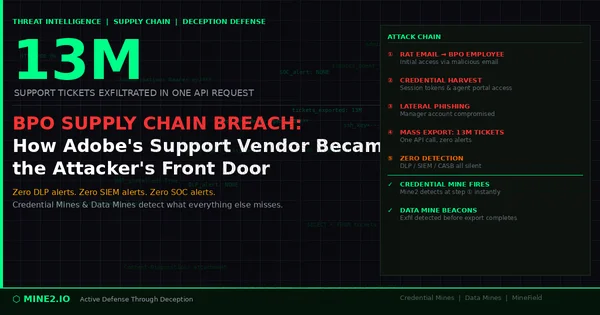
13 Million Tickets, One Request: How the Adobe BPO Breach Exposes the Third-Party Credential Blind Spot
Need Security Help?
Protect your organization with MINE2's cyber deception platform.