HeartCrypt-Packed EDR Killer (AVKiller): The New Weapon in Ransomware Campaigns
Date: August 8, 2025
Ransomware campaigns continue to evolve, and a new threat has emerged that poses a serious risk to organizations and their endpoint security defenses. In August 2025, Sophos X-Ops uncovered a rising cyber threat where ransomware operators are utilizing a sophisticated tool called HeartCrypt, a packer-as-a-service (PaaS), to actively disable Endpoint Detection and Response (EDR) and antivirus (AV) products before deploying their ransomware payloads.
This marks a significant shift in ransomware tactics, highlighting the growing trend of cybercrime-as-a-service and the collaborative tool-sharing among different threat groups.
Origins and Evolution of HeartCrypt
HeartCrypt was designed and engineered by RansomHub, evolving directly from the notorious EDRKillShifter tool used in previous campaigns. Its arrival signifies a dangerous escalation, as at least eight ransomware groups—including RansomHub, Blacksuit, MedusaLocker, Qilin, DragonForce, Crytox, Lynx, and INC—are actively deploying HeartCrypt in their attacks.
This tool is a perfect example of cybercrime-as-a-service, where different threat actors leverage shared tools and resources. What's even more troubling is the semi-coordinated nature of the tool's proliferation. Through customized builds, shared obfuscation strategies, and even tool reselling, HeartCrypt has quickly become a favorite among major cybercriminal groups.
How HeartCrypt Works: Technical Execution
HeartCrypt is a highly effective EDR/AV killer, which works by injecting malicious code into legitimate, signed executables. Here's how it functions:
1. Delivery Method
- Ransomware groups deploy HeartCrypt via EDR killer droppers or trojanized utilities. A prime example is using legitimate tools like Beyond Compare's Clipboard Compare tool, which is compromised to carry malicious payloads.
2. Payload Execution
- Once the malicious payload is executed, it decodes itself and launches an obfuscated binary.
- The binary then searches for a five-letter driver (e.g., mraml.sys, noedt.sys) signed with either compromised or expired certificates.
- Through a technique known as BYOVD (Bring Your Own Vulnerable Driver), HeartCrypt loads a kernel driver impersonating trusted security software, such as CrowdStrike Falcon Sensor.
3. EDR/AV Termination
- Once the driver is loaded into the kernel, it begins terminating EDR and AV processes, effectively disabling endpoint defenses and leaving the system vulnerable to further ransomware deployment.
4. Obfuscation and Evasion
- HeartCrypt uses multi-stage packing and resource encryption, making detection by traditional static or behavioral analysis tools almost impossible.
Targeted Security Products
HeartCrypt is capable of disabling leading endpoint protection solutions, including:
- Sophos
- Microsoft Defender
- Kaspersky
- Trend Micro
- SentinelOne
- McAfee
- Bitdefender
- Cylance
- F-Secure
- Symantec
- Webroot
- HitmanPro
...and many others.
The Impact on Defenders
One of the most concerning aspects of HeartCrypt is its ability to disrupt dynamic shellcode detection and bypass device control mechanisms. RansomHub demonstrated how this capability can be used to deploy ransomware quickly and stealthily, with minimal chance of detection or response.
Sophos X-Ops researchers noted that each attack using HeartCrypt involved unique, group-specific builds, signaling that these attacks were carefully planned and executed—rather than being opportunistic uses of off-the-shelf tools. This highlights the increasing sophistication and organization behind ransomware campaigns.
Strategic Challenges for Defenders
1. Accelerated Attack Chains
The commoditized nature of HeartCrypt, along with its widespread adoption across various ransomware groups, has accelerated attack chains. This collaborative underground ecosystem mimics legitimate software development processes and makes detection and mitigation much harder.
2. Erosion of Trust in Driver Signing
The use of expired or stolen legitimate certificates to sign drivers (BYOVD attacks) undermines trust in the driver-signing model. This erodes confidence in traditional methods of validating software legitimacy.
3. AI and Automation Limitations
The use of advanced techniques such as custom obfuscation, BYOVD, and deep encryption demonstrates that AI-based security solutions alone may not be enough to detect such sophisticated, tailored threats. Layered, adaptive security controls are now more crucial than ever.
Mitigation Recommendations
To protect against HeartCrypt-packed EDR killers and similar threats, organizations should consider the following actions:
- Patch and monitor remote access tools, such as SimpleHelp, to prevent unauthorized access.
- Enforce strict driver-signing policies, and configure alerts for revoked/expired/untrusted driver certificates.
- Set up alerts for mass termination of security processes and services, which can help detect suspicious activities early.
- Deploy robust application allowlisting, especially for binaries in user or temp directories, to block unauthorized executables from running.
- Train your security teams to recognize anomalous driver behaviors and signs of EDR tampering.
- Regularly run red-team simulations to test your resilience against EDR-killing techniques and BYOVD attacks.
- Leverage Indicators of Compromise (IOCs) provided by security vendors to proactively block known threats.
- Adopt AI-enhanced detection systems and embrace Zero Trust principles across your security stack to reduce risk.
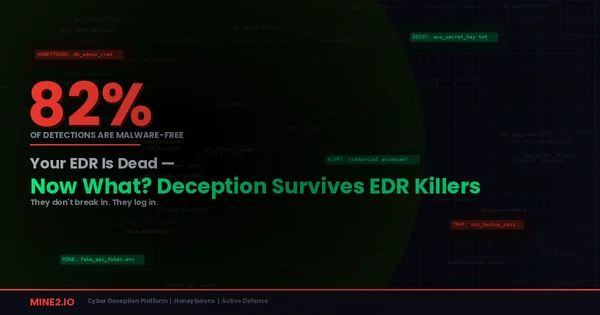
MINE2's Perspective
HeartCrypt represents exactly the type of sophisticated threat that traditional EDR solutions struggle to detect and prevent. This is where cyber deception technology becomes critical:
How MINE2 Can Help:
- Deception-based detection that doesn't rely on signatures or behavioral patterns
- Honeypot systems that can detect attacker presence even after EDR termination
- Credential honeytraps that alert when attackers attempt lateral movement
- Network deception that remains active even when endpoint agents are disabled
Learn more about protecting against EDR killers with MINE2's deception platform.
Key Takeaways
The emergence of HeartCrypt-packed AVKiller signals a new wave of ransomware toolkits that empower cybercriminals with advanced capabilities to disable endpoint defenses. The BYOVD exploits and deep obfuscation techniques used by HeartCrypt allow attackers to bypass even the most robust endpoint protections—often going undetected until it's too late.
The collaboration among different ransomware groups and the tool-as-a-service model used by criminals make the job of defending against these threats harder than ever. To stay ahead, organizations need proactive, layered defenses, including continuous patching, driver signing enforcement, security team training, and the adoption of adaptive security strategies.
In the face of such evolving threats, a holistic security approach—comprising regular patching, policy enforcement, advanced detection mechanisms, and layered Zero Trust defenses—is essential for building resilience in 2025 and beyond.
References & Further Reading
- Sophos X-Ops Report: "Shared Secret: EDR Killer in the Kill Chain"
- SC Media / BleepingComputer: Coverage on Tool Adoption by Ransomware Groups
- Security Boulevard / Sophos: Analysis of Tool-Sharing and HeartCrypt Usage
- Cybersecurity News: Detailed AVKiller Behavior and Impact
- Palo Alto Networks Unit42 Threat Blog: Ransomware Evolution
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
Need Security Help?
Protect your organization with MINE2's cyber deception platform.