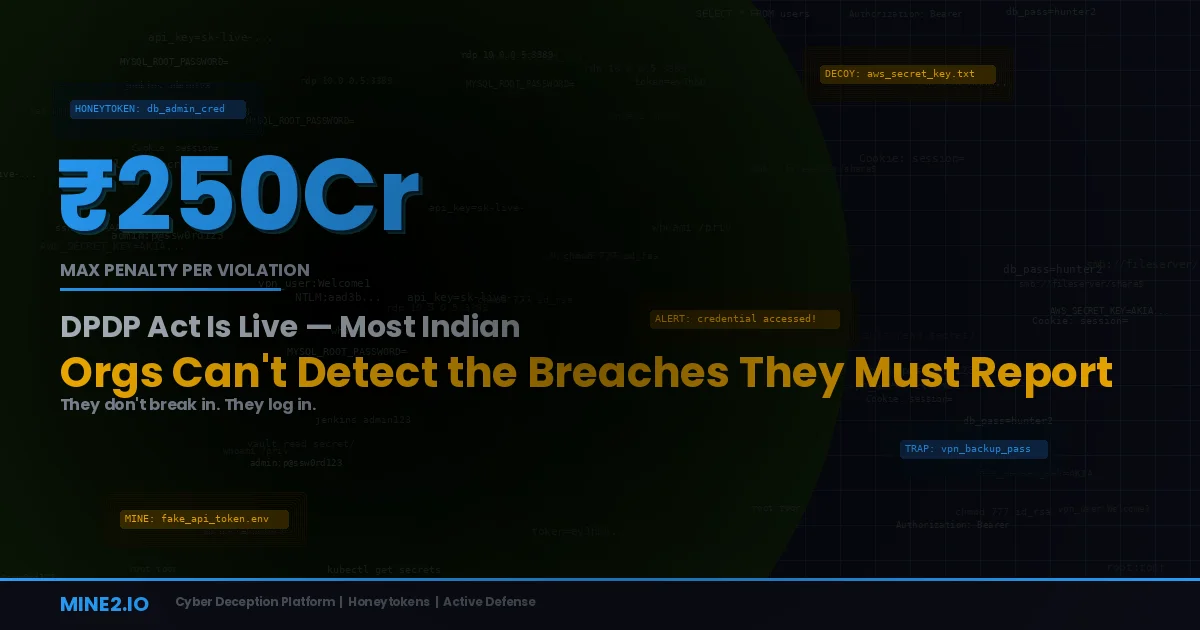
On November 13, 2025, India's Digital Personal Data Protection Rules went live — transforming the DPDP Act 2023 from legislative principle into enforceable reality. Organizations now have until May 13, 2027 to achieve full compliance. After that, there's no grace period. Penalties kick in from day one.
The numbers are stark: up to ₹250 crore for failure to implement reasonable security safeguards. Up to ₹200 crore for failing to notify the Data Protection Board of India (DPBI) and affected individuals of a breach. Up to ₹200 crore for processing without valid consent. Multiple violations compound — each infraction carries its own penalty.
Here's the problem no one is talking about: you can't notify a breach you never detected.
India's cybersecurity incident count more than doubled from 1.03 million in 2022 to 2.27 million in 2024. Malware detections surged from 5 million in 2021 to 53 million in 2024 — a tenfold increase in three years. The BFSI sector alone faced an average of 4.1 million attacks monthly in the first half of 2025. And IBM pegs the average cost of a data breach in India at approximately ₹220 million, even before DPDP penalties are layered on top.
Yet the average time to identify and contain a breach globally remains close to 240 days. In India's critical sectors — healthcare (21% of malware cases), BFSI (19%), hospitality (17%), and education (15%) — outdated infrastructure and underfunded security teams mean detection gaps are often even wider.
The DPDP Act doesn't just ask you to protect data. It asks you to know when protection fails, and to tell the regulator immediately. For most Indian organizations, that capability simply doesn't exist today.
What the DPDP Rules Actually Require — And Where the Gaps Are
The DPDP Rules 2025 create specific, enforceable obligations around security and breach detection that go far beyond previous CERT-In requirements.
Reasonable security safeguards (Rule 6). Data Fiduciaries must implement appropriate technical and organizational measures to prevent personal data breaches. The Rules explicitly reference encryption, access control, authentication, event detection, logging, backups, and monitoring. This isn't a suggestion — it's a mandatory baseline, and failure carries the highest penalty tier of ₹250 crore.
Mandatory breach notification — with no materiality threshold. Unlike GDPR, which requires notification only when a breach is "likely to result in a risk to the rights and freedoms of natural persons," the DPDP Rules contain no threshold for breach reporting. On a strict reading, every personal data breach must be reported to the DPBI and affected Data Principals. This is an extraordinarily aggressive notification requirement — and it means organizations need detection capabilities that catch breaches of any scale.
CERT-In's six-hour reporting window still applies. India's CERT-In directive already mandates reporting cybersecurity incidents within six hours of detection. For BFSI entities under RBI and SEBI oversight, additional sector-specific breach reporting requirements layer on top. The DPDP Act adds another reporting obligation to the DPBI. Organizations now face parallel notification requirements across multiple regulators — all triggered by the ability to detect a breach in the first place.
Minimum one-year log retention. The Rules mandate maintaining security logs for at least one year, supporting audit trails and forensic investigation. This means organizations need not just detection but a provable record of their detection capabilities.
Significant Data Fiduciaries face enhanced scrutiny. Organizations classified as Significant Data Fiduciaries (SDFs) — including e-commerce platforms with 20 million+ Indian users, online gaming platforms with 5 million+ users, and entities processing large-scale behavioral or sensitive data — face mandatory audits, Data Protection Impact Assessments, and continuous compliance monitoring. For SDFs, the cost of a detection gap is multiplied by regulatory examination.
India's Detection Problem Is a Compliance Crisis
Let's be direct about the state of breach detection in India's most regulated sectors.
BFSI is under siege. The banking sector saw 248 data breaches across scheduled commercial banks over a four-year period. Supply chain attacks through vendor portals have become the preferred entry point — the ICICI Bank incident involved credential harvesting through a compromised third-party vendor. A Nupay breach exposed 273,000 bank transfer documents through a misconfigured S3 bucket. The LIC database — allegedly containing 454 million rows of policy data — was advertised for sale on dark web forums. And following geopolitical tensions, over 1.5 million cyberattacks targeted Indian critical infrastructure, with seven APT groups identified.
Healthcare can't protect patient data. The ICMR breach exposed data on 815 million citizens. Delhi hospitals had patient records, financial data, and administrative files accessed after server hacking. Healthcare accounted for 21% of all malware detections in India — the highest of any sector. Under the DPDP Act, every one of these incidents requires notification to the DPBI and affected individuals.
The talent gap cripples detection. 68% of Indian companies admit incomplete understanding of their DPDP obligations. The cybersecurity talent shortage means most organizations lack dedicated SOC teams capable of 24/7 monitoring. When your security team is understaffed and overwhelmed with alerts, breaches that use valid credentials or exploit third-party access go undetected for months.
Third-party risk is the blind spot. Multiple major Indian breaches in 2025 originated from compromised vendor portals and misconfigured cloud services — not direct attacks on the organization itself. Under the DPDP Act, the Data Fiduciary is responsible regardless of whether the breach occurred at a processor or vendor. You can't delegate the penalty.
How Mines Solve the DPDP Detection Gap
This is where cyber deception — specifically Mine2's Mines — becomes a direct compliance enabler.
Mines are decoy assets planted throughout your environment: fake credentials, bogus documents, decoy services, and phantom cloud resources. No legitimate user or process should ever interact with a Mine. Any interaction is, by definition, a breach indicator — providing immediate, zero-false-positive detection that satisfies the DPDP Act's requirement for event detection and reasonable security safeguards.
Here's why Mines are uniquely suited to India's DPDP compliance challenge:
Mines Detect Breaches That Traditional Tools Miss
The DPDP Act requires you to detect every personal data breach — not just the ones that trigger your SIEM rules. When an attacker uses valid credentials harvested from a third-party vendor breach, your EDR sees a legitimate login. Your SIEM sees authorized access. There's no alert.
Mines change this equation. Credential Mines planted in credential stores, config files, and documentation catch credential harvesting. Data Mines scattered across file shares and databases catch unauthorized data enumeration. MineField decoy services catch network reconnaissance. Any attacker who enters your environment — regardless of how legitimate their access appears — will inevitably encounter a Mine during their exploration. The alert fires immediately. Zero false positives. No behavioral baseline required.
For DPDP compliance, this means you can detect breaches that would otherwise go unreported — not because you chose not to report them, but because you never knew they happened.
Mines Satisfy "Reasonable Security Safeguards"
Rule 6 of the DPDP Rules requires encryption, access control, authentication, event detection, logging, and monitoring. Mine2's platform directly addresses the event detection and monitoring requirements by providing a detection layer that:
- Generates immediate alerts on unauthorized data access (supporting CERT-In's six-hour reporting window)
- Produces forensically rich logs showing exactly what was accessed, when, and from where (supporting the one-year log retention requirement)
- Operates with zero false positives (meaning every alert is actionable, critical for understaffed Indian SOC teams)
- Requires no behavioral baselines or tuning (deployable within hours, critical given the May 2027 compliance deadline)
When the DPBI investigates a breach, the question they'll ask is: what safeguards did you have in place? Mines demonstrate a proactive, industry-leading detection capability that goes beyond the minimum — exactly the kind of "reasonable safeguard" the Act envisions.
Mines Protect What BFSI and Healthcare Regulators Care About Most
For BFSI organizations under RBI oversight, the critical assets are customer account data, transaction records, and financial credentials. Mine2 Mines planted alongside these assets — fake account records in databases, decoy transaction logs, honeytoken API keys for banking APIs — create a detection perimeter around the data the regulator cares about most.
For healthcare organizations, Mines planted as decoy patient records, bogus clinical trial databases, and fake administrative credentials detect unauthorized access to protected health information. When the DPBI asks how you detected a breach involving patient data, "our Mines triggered when the attacker accessed decoy records" is a far stronger answer than "we found out from a dark web monitoring service three months later."
Mines Enable Faster Breach Notification
The DPDP Act's breach notification requirement has teeth precisely because delayed notification compounds harm. Every day an organization doesn't know about a breach is a day that stolen data is being monetized, shared, or weaponized.
Mines collapse detection time from months to minutes. The moment an attacker interacts with a Mine, you know:
- That a breach is occurring (triggering notification obligations)
- What type of data is at risk (informing the scope of notification)
- Where the unauthorized access originated (supporting forensic investigation)
- Which systems are compromised (enabling targeted containment)
This information is exactly what the DPBI and CERT-In need in a breach notification — and Mines provide it in real time rather than after a months-long forensic investigation.
Cloud Mines Cover India's Cloud Compliance Challenge
As Indian organizations migrate to AWS, Azure, and GCP, cloud-hosted personal data falls under DPDP jurisdiction regardless of where the cloud infrastructure is physically located. Cloud misconfigurations and IAM exploitation accounted for 62% of detections in Indian cloud environments according to DSCI.
Mine2's Cloud Mines deploy fake resources — decoy S3 buckets, phantom IAM roles, bogus Lambda functions — across cloud environments. When a misconfigured access policy or compromised cloud credential leads to unauthorized resource enumeration, Cloud Mines detect it before real personal data is accessed.
Practical Playbook: Mines for DPDP Compliance
Phase 1: Immediate (Now through November 2026)
Deploy Credential Mines across high-value systems. Start with the systems that process the most personal data: CRM databases, HR systems, patient management platforms, banking core systems. Plant fake credentials in locations where attackers and infostealers harvest: browser stores, config files, environment variables, documentation wikis.
Deploy MineField on network segments hosting personal data. Place decoy services adjacent to database servers, file shares, and application servers that process personal data. Any reconnaissance targeting these segments will trigger immediate detection.
Integrate Mine alerts with your incident response workflow. Ensure every Mine alert triggers your breach notification checklist — including parallel notifications to CERT-In (six hours) and DPBI preparation.
Phase 2: Implementation (March 2026 — May 2027)
Extend Mines to third-party access paths. Plant Mines on network segments accessible to vendors, contractors, and cloud service providers. Third-party breaches are the dominant entry vector for Indian organizations — Mines on vendor-accessible segments detect compromised access before it reaches production data.
Deploy Cloud Mines across your AWS/Azure/GCP footprint. Focus on IAM enumeration paths, S3/Blob discovery, and cross-account trust boundaries. Ensure coverage of all cloud-hosted personal data stores.
Harden with Fortify. Use Mine2's Fortify to close misconfigurations, restrict unnecessary access, and eliminate privilege escalation paths. Layer Mines on top of hardened infrastructure — so that even if an attacker bypasses a control, the next step they take triggers a detection.
Establish audit trail documentation. Mine2's alert logs, deployment records, and detection reports provide the documented evidence of "reasonable security safeguards" that the DPBI will request during an investigation.
Phase 3: Continuous Compliance (Post May 2027)
Rotate and refresh Mines regularly. Update decoy credentials, refresh fake records, and reposition MineField services to maintain detection effectiveness against persistent threats.
Conduct regular Mine-triggered detection drills. Test your notification workflow end-to-end: Mine alert → investigation → CERT-In notification → DPBI notification → affected individual notification. Prove the process works before a real breach forces you to use it.
Include Mine deployment in SDF audit documentation. For Significant Data Fiduciaries, Mine2 deployment demonstrates a proactive, beyond-minimum-baseline approach to breach detection — exactly what auditors and the DPBI expect to see.
The Bottom Line
The DPDP Act 2025 has changed the game for Indian organizations. It's no longer enough to build walls around personal data. You need to know — immediately — when those walls are breached. With penalties up to ₹250 crore and no materiality threshold for breach notification, the cost of not knowing is now regulatory as well as operational.
India's breach detection reality — 240-day dwell times, 53 million malware detections, vendor-portal attacks, understaffed SOC teams — makes the DPDP Act's notification requirements practically impossible to meet with traditional security tools alone.
Mines solve this. They detect breaches at the moment of unauthorized access, with zero false positives, no behavioral baselines, and deployment timelines measured in hours rather than months. For BFSI institutions under RBI oversight, healthcare organizations protecting patient data, e-commerce platforms managing millions of user records, and every Data Fiduciary racing toward May 2027 compliance — Mines aren't just a security tool. They're a DPDP compliance enabler.
The clock is ticking. The DPBI is operational. The penalties are real. The question isn't whether you'll face a breach — it's whether you'll detect it in time to meet your notification obligations.
Ready to close the DPDP detection gap? See how Mine2's Mines provide zero-false-positive breach detection →
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
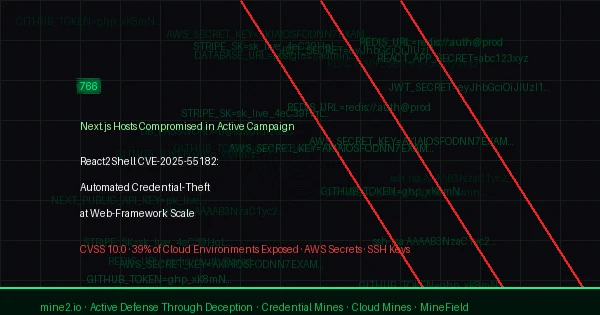
React2Shell CVE-2025-55182: 766 Next.js Hosts Breached in Automated Credential-Theft Wave
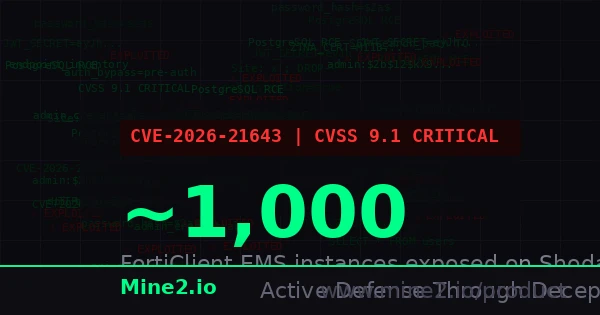
FortiClient EMS Under Fire: CVE-2026-21643 Turns Endpoint Management Into an Attacker's Credential Goldmine
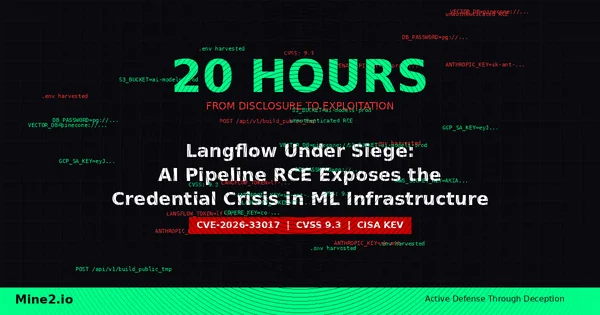
Langflow Under Siege: AI Pipeline RCE Exploited in 20 Hours Exposes the Hidden Credential Crisis in ML Infrastructure
Need Security Help?
Protect your organization with MINE2's cyber deception platform.