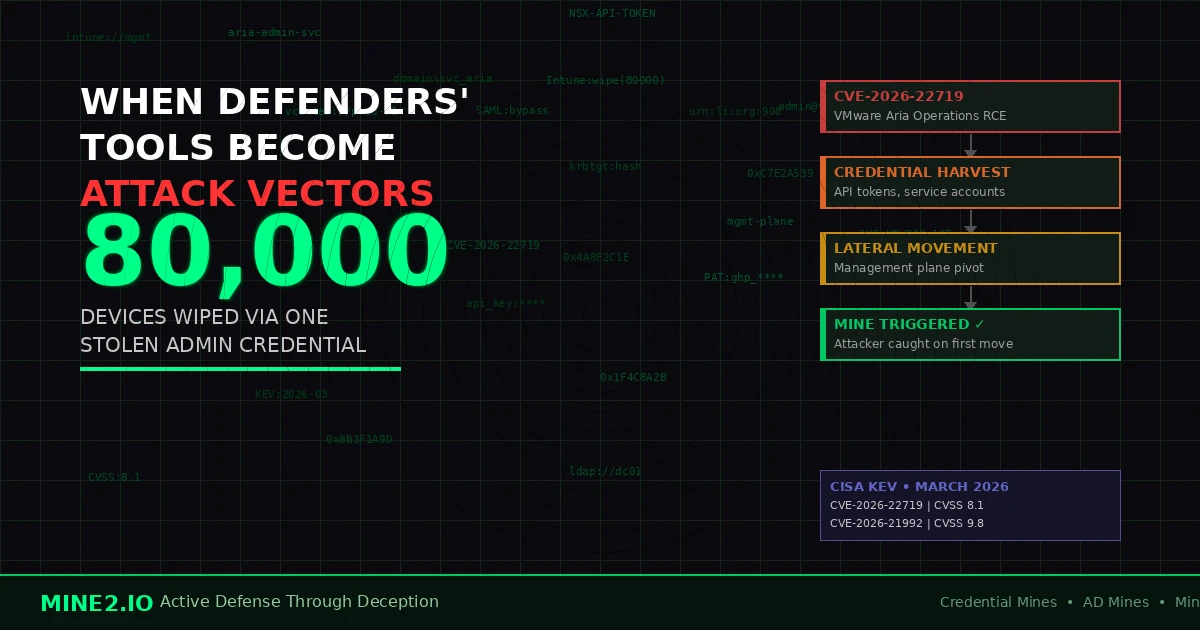
There is a brutal irony at the heart of enterprise security in 2026: the platforms your team relies on to detect, manage, and respond to threats have become the highest-value targets for attackers. When CISA added CVE-2026-22719 — a command injection flaw in VMware Aria Operations — to its Known Exploited Vulnerabilities catalog on March 3, 2026, it wasn't a surprise to threat intelligence analysts. It was confirmation of a trend that has been building for two years: attackers have systematically turned their attention from endpoints to the administrative platforms that govern them all.
VMware Aria Operations is not a peripheral tool. It is the observability and management backbone for tens of thousands of enterprise VMware environments. Compromise it, and you gain visibility into every workload, every configuration, and every credential stored within. The CVSS score for CVE-2026-22719 is 8.1, but the operational blast radius of exploitation is orders of magnitude higher. Federal civilian agencies were given until March 24, 2026 to apply fixes — a timeline that tells you everything about the urgency CISA assigns to this class of vulnerability.
This post examines why management platforms have become the primary beachhead in advanced attacks, why your existing security controls struggle to detect the post-exploitation phase, and how deception technology — specifically Credential Mines and AD Mines — closes the detection gap that every other tool leaves open.
The Management Platform Is Now the Crown Jewel
Attackers have always followed value. For years, that meant targeting endpoint devices, then moving laterally to find sensitive data. The calculus changed when enterprises invested heavily in endpoint detection and response. Today, a compromised laptop generates dozens of alerts within minutes. But a compromised VMware Aria administrator account? That can go undetected for weeks.
The Stryker attack in March 2026 is the definitive case study. An Iran-aligned hacktivist group obtained a single compromised Microsoft Intune administrator account and, from that single foothold, remotely wiped approximately 80,000 devices across Stryker's global network — simultaneously, in real time. Employees watched their computers erase themselves. The attack did not require malware deployed to endpoints. It did not require lateral movement through workstations. It required one set of management credentials and knowledge of how to use the platform's own APIs against the organization that built it.
This is the attacker's insight: management platforms are designed for scale. They can push policy to 80,000 devices just as easily as they can push it to one. When an attacker obtains management credentials, they inherit that scale. Traditional endpoint security tools are irrelevant — the destruction happens through legitimate platform functionality.
The pattern extends beyond Intune. In the same month, Oracle released patches for CVE-2026-21992 in Identity Manager — a critical flaw with a CVSS score of 9.8 enabling unauthenticated remote code execution against the identity and access management platform that governs who can authenticate to everything else in the enterprise. When your identity management system is the breach, no authentication event is trustworthy. Active Directory, LDAP, SAML federation — all compromised at the source.
Why This Threat Pattern Is Accelerating
Three structural forces are converging to make management platform exploitation the dominant attack vector of 2026.
First, security teams have successfully hardened the endpoint perimeter. Investment in EDR, privileged access workstations, and credential hygiene at the workstation level has raised the cost of traditional lateral movement. Attackers have responded rationally: target the management layer instead.
Second, management platforms have accumulated extraordinary privilege as enterprises consolidated tooling. Aria Operations manages infrastructure. Intune manages endpoints. Oracle Identity Manager manages authentication. Centralization improves operational efficiency and creates a catastrophic single point of compromise. The Datadog DevSecOps 2026 Report found that 57% of organizations reported experiencing a security incident based on exposed secrets from insecure management and DevOps processes in the prior two years.
Third, these platforms are structurally difficult to monitor from the outside. You cannot deploy a third-party agent onto Aria Operations. You cannot instrument every API call within Intune without performance implications. The platforms that are supposed to be watching everything have the smallest amount of scrutiny applied to their own activity.
What the Attack Chain Looks Like
The typical management platform compromise in 2026 follows a predictable sequence that illustrates exactly why detection is difficult.
Initial access arrives via one of three pathways: exploitation of an unpatched vulnerability (CVE-2026-22719 being the most recent example), theft of a service account credential from a CI/CD pipeline or secrets manager, or phishing a platform administrator whose multi-factor authentication was bypassable via session token hijacking. CISA's analysis of the SharePoint RCE vulnerability CVE-2026-20963 — also added to the KEV catalog in March 2026 — shows a parallel pattern where productivity platforms with deep Active Directory integration become access pathways to identity systems.
Once inside the management platform, the attacker's first move is consistent: credential harvesting. Aria Operations stores API tokens, vCenter service account credentials, NSX integration certificates, and SMTP relay credentials. Identity Manager stores every service account, privileged user, and application integration secret in the environment. The attacker's goal is to harvest these credentials silently — not to deploy ransomware immediately, but to build a complete map of the privilege estate before making any visible move.
The second phase is persistence establishment. Using the management platform's own native capabilities, attackers create backdoor accounts, modify monitoring rules to exclude their activity, and establish scheduled tasks that will survive a password reset of the initially compromised account. The Stryker attack demonstrated a third-phase execution where destruction was the goal; in financially motivated attacks, this phase is typically lateral movement to financial systems or data repositories.
The critical detection window is the credential harvesting phase. Attackers are accessing stored credentials, attempting to authenticate using those credentials against other systems, and probing the credential store for additional accounts. This is where deception technology turns the attacker's methodology against them.
Why Traditional Controls Fail at the Management Layer
Every enterprise security architecture assumes a trust boundary: the tools doing the monitoring are trusted, the systems being monitored are not. Management platform exploitation breaks this assumption completely.
Your SIEM ingests logs from Aria Operations. When an attacker uses an Aria administrator account, the activity looks legitimate — the SIEM has no baseline for what "abnormal" Aria administrator behavior looks like, because administrator behavior is inherently variable. Your PAM solution may wrap access to Aria itself, but once inside, the attacker can generate API tokens that bypass PAM entirely. Your EDR cannot see activity that happens within the management plane rather than on endpoints.
The deeper problem is signal quality. CISA's investigation into CVE-2026-22719 exploitation found that in the majority of confirmed incidents, the attack had been underway for 14 to 21 days before detection. In every case, the management platform's own logs contained indicators — anomalous API calls, unusual credential access patterns, authentication from unexpected source IPs — but the sheer volume of legitimate management activity buried the signal. Security operations teams reviewing hundreds of events per hour cannot reliably surface the specific pattern that indicates credential harvesting within a management console.
This is not a resourcing problem. It is a fundamental signal-to-noise problem that cannot be solved by adding more analysts or tuning more SIEM rules. You need a control that generates an unambiguous, zero-false-positive alert the moment an attacker touches it.
How Credential Mines and AD Mines Break the Attack Chain
Mine2's deception technology applies a simple but powerful principle to the management platform problem: plant credentials that look real but have never been used for legitimate purposes, and monitor them for any access. The first access to a mine is always an attacker — because no legitimate process ever touches it.
Credential Mines planted within VMware Aria Operations take the form of stored API tokens, vCenter service account entries, and integration credentials that appear to belong to real systems but route to mine detection infrastructure. When an attacker harvests credentials from Aria and attempts to use them — whether to authenticate to vCenter, call an AWS API, or connect to a database — the mine triggers a high-fidelity alert. Not a suspicion. Not a risk score. A confirmed breach event, timestamped to the minute of first use.
AD Mines address the identity management attack vector directly. When an attacker compromises Oracle Identity Manager or extracts credentials from Active Directory via a management platform integration, they are looking for privileged accounts to impersonate: service accounts with domain admin rights, application integration accounts with broad read access, administrator accounts associated with security tooling. AD Mines are purpose-built to look exactly like these accounts. They have realistic naming conventions, appropriate group memberships, and last-login timestamps that establish credibility. Any attempt to authenticate as a mine account — via Kerberos, LDAP, NTLM, or SAML — generates an immediate alert with full attribution: source IP, timestamp, authentication method, and lateral movement destination.
MineField decoy services address the network discovery phase. Before an attacker uses harvested credentials, they typically probe the network to understand the topology — which management consoles are accessible, what APIs respond on which ports, where RDP is available on management workstations. MineField plants decoy TCP services on ports and addresses that no legitimate system should be scanning. The first probe is an alert.
The operational advantage of this approach is that it requires no tuning, no baseline establishment, and no alert fatigue management. A mine either triggers or it doesn't. When it triggers, the event is not a hypothesis — it is a confirmed breach event that immediately initiates the incident response workflow.
Compliance Implications: When the Management Platform Is Breached, the Reporting Clock Starts Immediately
Management platform compromises create immediate and severe compliance exposure because of what these platforms can access. A breach of Aria Operations or Oracle Identity Manager is not a breach of one system — it is a potential breach of every system those platforms manage, authenticate, or store credentials for.
GDPR Articles 33 and 34 require notification to supervisory authorities within 72 hours of becoming aware of a personal data breach, and notification to affected individuals when the breach is likely to result in high risk. When a management platform is compromised, the scope of potentially affected personal data — stored in managed systems, accessible via managed credentials — is vast, and the 72-hour clock begins at awareness. Mine2's detection evidence provides the precise timestamp of first attacker activity, which is critical for demonstrating awareness timelines to regulators.
India's Digital Personal Data Protection Act (DPDP Act) requires data fiduciaries to notify the Data Protection Board and affected data principals "without delay" upon becoming aware of a personal data breach. Management platform compromises in environments processing Indian citizen data trigger these obligations immediately. Mine2's mine triggers provide the timestamped evidence of breach discovery that the DPDP reporting process requires.
PCI-DSS Requirement 11 mandates the testing of security controls and monitoring of all access to network resources and cardholder data. Management platform credentials with access to payment processing infrastructure create direct PCI scope implications. The audit trail generated by Mine2 mine triggers provides the evidence of detection capability that Requirement 11 audits require.
CERT-In's 6-hour reporting mandate — arguably the most aggressive breach reporting requirement globally — requires Indian organizations to report any breach within six hours of discovery. Mine2's real-time alerting ensures that discovery happens at the moment of first attacker activity, not weeks later during a forensic investigation. The difference between detecting a breach in six minutes via a mine trigger and detecting it in 14 days via log analysis is the difference between compliance and a reportable violation.
SEBI and RBI directives for regulated financial entities in India require robust controls over privileged access and management infrastructure. Mine2's mine deployment within management platforms provides the evidence of active deception-based monitoring that these frameworks increasingly recognize as a best-practice detection control.
HIPAA requires covered entities and business associates to implement technical safeguards that control access to electronic protected health information and to audit activity in systems containing ePHI. Management platforms with access to healthcare IT environments fall within scope, and mine triggers provide the access monitoring evidence required by the Security Rule.
The Practical Playbook: Protecting Your Management Stack with Deception
Organizations looking to close the management platform detection gap should implement the following deception-forward strategy.
The first priority is inventory. Map every management platform in the environment — VMware Aria Operations, Microsoft Intune, ServiceNow, Splunk infrastructure, identity management systems, PAM consoles — and identify what credentials each platform stores or can generate. This inventory defines your mine placement strategy.
The second step is mine deployment within each platform. In Aria Operations, plant Credential Mines that look like vCenter integration accounts and NSX service tokens. In Active Directory and identity management systems, deploy AD Mines that look like platform service accounts. In PAM vaults, create mine accounts that appear to be high-privilege emergency access credentials. Mine2's single-click deployment model means this step takes minutes, not weeks.
The third step is establishing the detection-to-response workflow. When a mine triggers, the response should be immediate: isolate the management platform session, rotate all credentials stored within the platform, initiate forensic collection from the platform's activity logs for the window preceding the mine trigger, and begin scope assessment of what managed systems may have been accessed. The mine trigger tells you that an attacker has credentials — the forensic investigation tells you what else they took.
The fourth step is establishing a regular mine rotation schedule. Credential mines should be refreshed periodically to ensure their appearance remains credible. Mine2's automated rotation capability handles this without operational overhead.
The Detection Gap Is Not Acceptable
The March 2026 vulnerability disclosures — CVE-2026-22719 in VMware Aria Operations, CVE-2026-21992 in Oracle Identity Manager, the ongoing exploitation of SharePoint and other management platform vulnerabilities — represent a trend that will not reverse. Attackers have learned that management platforms are the leverage point for maximum impact at minimum cost. One compromised Intune administrator account cost Stryker the wipe of 80,000 devices. One compromised Aria Operations instance yields the credential estate for an entire VMware environment.
The organizations that detected these compromises early — before destructive execution, before mass data exfiltration — were the organizations that had controls in place that generated unambiguous signals the moment stolen credentials were first used. Detection through tuned SIEM rules, behavioral analytics, or log review is fundamentally too slow for this threat. By the time anomaly-based detection fires, the attacker has had days or weeks of dwell time.
Credential Mines and AD Mines deployed within management platforms operate differently. They do not analyze behavior patterns. They do not require baseline establishment. They generate a single, high-fidelity alert the first time an attacker touches them — which, in the management platform context, is the moment stolen credentials are used for lateral movement. That is the earliest possible detection point, and it is the detection point that matters.
Conclusion
The weaponization of management platforms is not a temporary attacker preference. It is a structural response to improved endpoint security, and it will intensify as enterprises continue to consolidate administrative tooling. CVE-2026-22719 is not the last critical management platform vulnerability CISA will add to the KEV catalog this year. The Stryker incident is not the last time a management credential will be used to destroy infrastructure at scale.
The question for security teams is not whether management platforms will be targeted, but whether they will have the controls in place to detect the breach before the attacker executes. Deception technology — specifically, Credential Mines planted in the management layer and AD Mines mimicking privileged service accounts — provides the answer: immediate, zero-false-positive detection at the moment of first credential use.
Ready to close the management platform detection gap? See how Mine2 deploys Credential Mines and AD Mines across your management infrastructure in a single click: https://www.mine2.io/product
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
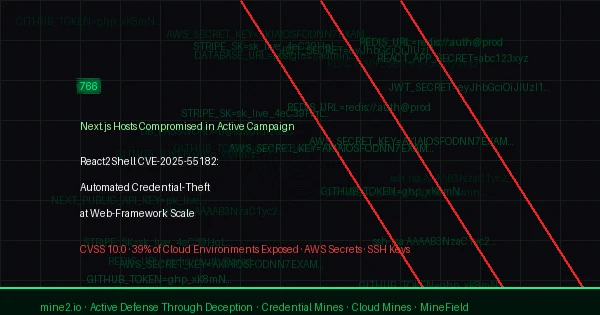
React2Shell CVE-2025-55182: 766 Next.js Hosts Breached in Automated Credential-Theft Wave
Kerberoasting in April 2026: Why CVE-2026-20833 Enforcement Is Not Enough Without AD Mines
The Service Account Blind Spot: How FortiGate Intrusions Expose the Lateral Movement Crisis
Need Security Help?
Protect your organization with MINE2's cyber deception platform.