A critical authentication bypass vulnerability in cPanel & WHM turned thousands of web hosting servers into easy targets for months before a patch arrived. Tracked as CVE-2026-41940 (CVSS 9.8), this flaw allowed unauthenticated remote attackers to gain full administrative access to control panels managing millions of websites.
Exploited in the wild since at least February 23, 2026 — nearly two months before cPanel's disclosure on April 28 — the bug exposed shared hosting environments to complete server takeovers, website defacements, ransomware deployment, and data theft.
This "zero to hero days" scenario highlights a painful truth: even mature software with millions of users can harbor dangerous flaws for extended periods. Traditional patching alone is no longer enough.
How the cPanel Zero-Day Worked
The vulnerability lived in the login flow. On a failed login attempt, cPanel wrote a pre-authentication session file to disk. Attackers could manipulate an authorization header (via CRLF injection) to inject credentials into this file, then force a reload — effectively logging in as an administrator without ever providing valid credentials.
Impact was severe:
- Full control over the cPanel host system
- Access to configurations, databases, and all hosted websites
- Potential compromise of every customer account on shared servers
With roughly 1.5 million internet-exposed cPanel instances at the time, the attack surface was enormous. Hosting providers like KnownHost, Namecheap, and HostPapa responded by temporarily blocking cPanel ports to buy time for patching.
WatchTowr Labs published technical analysis and a PoC shortly after disclosure, accelerating exploitation even further. Attackers wasted no time deploying Mirai variants and ransomware on compromised servers.
The Dangerous Gap Between Discovery and Detection
Zero-days like CVE-2026-41940 expose the limits of reactive security. Organizations waited weeks or months for patches while attackers operated freely. Even after disclosure, many servers remained unpatched due to update delays or legacy constraints.
Standard defenses — firewalls, WAFs, and endpoint protection — often miss these authentication bypasses because they appear as legitimate (or near-legitimate) login activity. By the time logs show anomalies, the damage is done.
How Mine2's Deception Layer Detects and Deflects These Threats
Mine2.io turns the attacker's reconnaissance and exploitation attempts into high-fidelity alerts using honeytokens, canary credentials, and breach traps.
In a cPanel/WHM environment, Mine2 would have provided early detection like this:
- Honeytoken Admin Sessions & Cookies — Fake session files and forged admin credentials planted in login paths. Any manipulation or injection attempt (like the CRLF technique) triggers immediate alerts.
- Canary Admin Accounts — Decoy administrator users with realistic permissions. When attackers use injected credentials to access these, Mine2 logs the activity and notifies teams before real accounts are touched.
- Breach Trap Control Panels — Decoy cPanel/WHM interfaces that mimic production. Attackers exploring post-bypass waste time on monitored traps, revealing their IPs, tools, and next moves while real systems stay protected.
- Automated Containment — Integration with SOAR playbooks enables instant actions: block IPs, isolate services, force credential rotations, or take decoy systems offline.
These deception elements work before patching is possible. Even during the two-month zero-day window, the first touch of a honeytoken would have exposed the attacker — turning silent exploitation into a detectable event.
Mine2 deploys with minimal overhead, zero false positives, and broad compatibility across hosting stacks. It complements patching cycles rather than replacing them.
Lessons for Hosting Providers and Enterprises
- Assume long zero-day windows — Critical flaws can remain undetected and unpatched for months.
- Layer detection beyond signatures — Behavioral deception catches what rules miss.
- Protect the control plane — cPanel, WHM, and similar management tools are high-value targets.
- Monitor for session anomalies — Especially around login flows and file writes.
The cPanel incident proves that speed of detection often matters more than speed of patching. With Mine2.io, organizations move from "zero to hero days" to detect and deflect in minutes.
Don't let the next zero-day become your organization's hero-day story.
Ready to close your zero-day detection gap? See how Mine2 deception works at mine2.io/product.
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
How to Safeguard Against Zero-Days: Lessons from Gladinet Triofox CVE-2025-12480
One Token, Dozens of Victims: How the Anodot SaaS Integration Breach Rewrites the Third-Party Risk Playbook
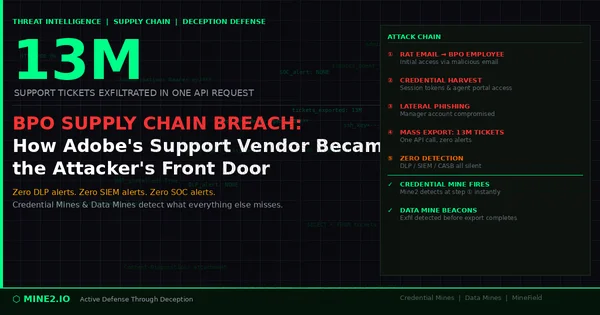
13 Million Tickets, One Request: How the Adobe BPO Breach Exposes the Third-Party Credential Blind Spot
Need Security Help?
Protect your organization with MINE2's cyber deception platform.