In early October 2025, the Crimson Collective—a newly emerged cybercrime group—disclosed a massive breach of Red Hat's consulting GitLab instance, claiming to have stolen 570GB of compressed data from over 28,000 repositories. This haul included sensitive Customer Engagement Reports (CERs) for roughly 800 organizations, spanning sectors like finance (Bank of America, JPMorgan Chase), tech (IBM, Cisco), government (U.S. Navy, NSA), and healthcare (Mayo Clinic). Red Hat confirmed the incident on October 2, emphasizing it was isolated to a consulting-specific GitLab setup, not their broader services or supply chain.

The breach's ripple effects are profound: attackers allegedly mined hardcoded secrets—API keys, database URIs, VPN configs—from CERs to pivot into client infrastructures. Belgium's cybersecurity center issued a high-risk advisory, urging credential rotations. For Red Hat customers, it's a scramble: audit logs, rotate tokens, scan repos. But this wasn't inevitable. Proactive deception could have detected the intrusion early, turning a supply-chain catastrophe into a contained alert.
A Rapid Rise and a Consulting Goldmine
Crimson Collective burst onto the scene on September 24, 2025, with a Telegram channel claiming a Nintendo defacement. By the next day, they hit Claro Colombia's telecoms. Then, on October 1, came Red Hat—escalating from vandalism to industrial-scale extortion.
The attack pattern mirrors consulting breaches we've seen before: unknown initial access (possibly phishing or a supply-chain vuln) led to data harvesting across repos. Attackers then sifted CERs for gems—infrastructure diagrams, vuln assessments, and especially secrets like cloud keys and DB strings. GitGuardian's research flags this as classic "secrets sprawl": internal repos hold 8-10x more embedded credentials than public ones, often from PoC code where consultants hardcode for speed.
Red Hat's response was swift but reactive: remediation underway, no evidence of wider impact. Yet the damage? Potential lateral moves into client networks, turning one breach into hundreds. As the group ignored private extortion overtures and went public, it exposed how consulting firms aggregate credentials like a digital vault—making them prime targets.
The Secrets Trap: Why Detection Lagged
Traditional security—firewalls, endpoint tools, even secrets scanners—relies on known threats or post-facto scans. In Red Hat's case, attackers operated with valid access, quietly exfiltrating for weeks. Hardcoded secrets went unnoticed until the Telegram post. No behavioral anomalies flagged bulk repo clones. No tripwires caught credential mining.
This is the blind spot: consulting engagements embed client PII and keys in shared repos, but without proactive lures, intruders roam freely. The result? A cascade: one firm's compromise unlocks doors at Boeing, Verizon, or the DoD.
Mine2: Deception That Stops the Cascade Before It Starts
Cyber deception flips the script—assuming breach and baiting attackers with fakes. Mine2.io deploys honeytokens, canary credentials, and breach traps seamlessly into GitLab, CERs, and downstream systems. Here's how it could have derailed Crimson Collective:
-
Honeytokens in CERs: Fake API keys, DB URIs, and VPN configs seeded across repos. Any query or export triggers a silent alert. Attackers "mine" decoys, revealing themselves during harvesting—before touching real Bank of America keys.
-
Canary Repos for Consulting: Decoy GitLab instances mimicking client projects, loaded with bogus infrastructure diagrams. Lateral movement into traps logs every pivot, buying time for isolation.
-
Breach Traps in Pipelines: Fake CI/CD configs with sham cloud access. If attackers test a "stolen" key, it routes to a monitored sinkhole, exposing IPs and tactics without risking production.
In practice: On initial access, a honeytoken touch alerts SecOps in minutes. Auto-rotate real credentials. Contain the GitLab instance. No 570GB exfil. No global advisories. For Red Hat customers, Mine2 integrates with SOAR to propagate deception downstream—e.g., fake tokens in rotated AWS keys.
Unlike noisy scanners, Mine2 generates zero false positives: only malice interacts with bait. Deployment? Non-disruptive, automated across 28,000+ repos.
From Reactive Rotations to Resilient Posture
Red Hat's breach is a stark reminder: supply chains aren't just code—they're credential webs. Organizations must treat consultants as extensions of their perimeter. Immediate steps include rotating all shared tokens and scanning for sprawl, but long-term? Layer in deception.
For consulting users: Mandate honeytokens in PoCs. For firms like Red Hat: Segregate repos, enforce customer secrets managers. With Mine2, breaches become intel opportunities—attackers reveal themselves, you respond faster.
The Crimson Collective's haul could fuel attacks for years. But with deception, it could have been a dud: fakes leading to dead ends. Don't wait for your Telegram moment. Build the traps now.
Mine2 Team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
Toyota's Sensitive Repo Was Publicly Exposed for 5 Years Before They Knew! How Can You Be Iron Sure to Not Repeat the Mistake?
We Will Ensure What Happened with Uber in 2022 Won't Happen to You
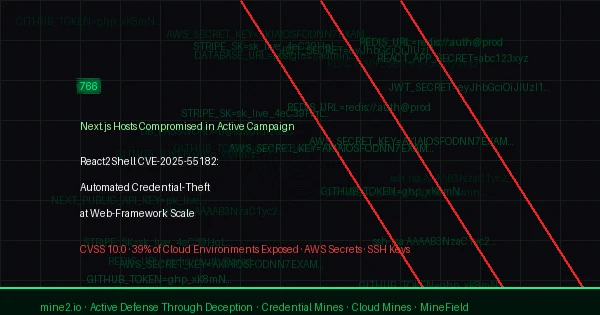
React2Shell CVE-2025-55182: 766 Next.js Hosts Breached in Automated Credential-Theft Wave
Need Security Help?
Protect your organization with MINE2's cyber deception platform.