Overview
In August 2025, financial institutions and fintech providers issued warnings regarding an emerging fraud scheme targeting Apple Pay and Google Pay—a technique known as ghost-tapping.
- First observed in Southeast Asia, ghost-tapping has now spread globally, driven by organized cybercrime syndicates coordinating through encrypted Telegram marketplaces.
- The method combines NFC relay attacks, phishing, SIM swapping, and money mule networks, turning stolen digital credentials into real-world purchases of luxury goods, electronics, jewelry, and even gold.
This represents the next evolution of mobile payment fraud, blending cyber-enabled theft with physical-world monetization.
What is Ghost-Tapping?
Ghost-tapping is a form of NFC relay fraud where attackers:
- Load stolen card data onto burner devices (low-cost phones with relay apps or proprietary hardware).
- Associate the data with Apple Pay or Google Pay wallets.
- Use NFC relay tools to make fraudulent in-person purchases at retail outlets or contactless ATMs.
The scheme professionalizes digital wallet abuse through automation, social engineering, and cross-border logistics, making detection and takedown highly complex.
Attack Lifecycle
1. Initial Access
- Phishing campaigns harvest credentials and OTPs.
- Mobile malware captures session cookies and payment info.
- SIM swap fraud exploits compromised telecom databases.
2. Exploitation
- Stolen card details are loaded into Apple Pay / Google Pay wallets.
- Attackers attempt to bypass banking security controls (example: DBS Bank fraud case).
3. Execution
- NFC relay fraud with tools like NFCGate (open source) or SuperCard X (commercial/proprietary).
- Mules purchase high-value items in physical stores.
- Some syndicates enable contactless ATM withdrawals.
4. Monetization
- Stolen goods resold via Telegram, Carousell, eBay, and Mercari.
- Proceeds laundered through USDT stablecoins and fiat cash-outs using mule networks.
Criminal Infrastructure
Telegram Marketplaces:
- Huione Guarantee – shut down May 2025; resurfaced in decentralized form.
- Xinbi Guarantee – escrow-driven USDT market.
- Tudou Guarantee – mule recruitment hub.
Relay Tools:
- NFCGate – open-source NFC relay app.
- SuperCard X – proprietary hardware/software sold via @webu8.
Notable Threat Actors
- @webu8 — developer of burner phones and proprietary relay software.
- @xingma888 — handler of mule crews in Singapore & Malaysia.
- 黑猫 (@llan19889) — recruiter of ATM mule networks.
- 路飞 (@OPLuffy888) — organizer of stolen goods transportation across borders.
Impact
- Financial Losses: High-value fraudulent purchases, gold/jewelry theft, ATM exploitation.
- Industries Affected: Retail, banking, fintech, insurance, digital wallet providers.
- Geographic Spread: Initially Southeast Asia (notably Singapore); now expanding worldwide.
- Scale: Example case — Between Oct–Dec 2024, 656 stolen cards in Singapore enabled nearly $930,000 USD in fraud.
Global Assessment
Ghost-tapping is a scalable and resilient fraud economy that:
- Evades legacy controls like SMS OTPs.
- Exploits weak wallet provisioning checks.
- Turns NFC relay tools + mule networks into repeatable fraud pipelines.
➡️ This is no longer niche — ghost-tapping is the next frontier of financial cybercrime.
Recommendations
For Banks & Payment Providers
- Enforce stronger KYC checks for wallet provisioning.
- Replace SMS or email OTPs with secure app-based push authentication.
- Deploy anomaly detection for device ID, IP, and geolocation patterns.
- Flag suspicious activity:
- Same card on multiple devices
- Single device linked to multiple cards
- Geo-distribution anomalies (e.g., same card in distant countries)
- Implement customer approval workflows during high-risk wallet additions.
For Consumers
- Enable MFA on all financial and email accounts.
- Never share OTPs or PINs; bank staff will never ask via SMS/phone.
- Beware phishing apps and fake install links; only download from official stores.
- Act fast — block compromised cards immediately upon suspicious alerts.
Conclusion
The rise of ghost-tapping fraud against Apple Pay and Google Pay marks a pivotal escalation in payment system abuse.
By leveraging NFC relay attacks, burner devices, and cross-border mule networks, cybercriminal syndicates are monetizing stolen digital credentials at scale, blending cybercrime with physical retail fraud.
Key Takeaway:
Banks, retailers, and consumers must treat mobile wallet fraud with the same urgency as digital banking risks. Stronger authentication, wallet governance, and fraud monitoring are critical to stopping ghost-tapping before it becomes a mainstream financial threat.
Mine2 Team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
One Token, Dozens of Victims: How the Anodot SaaS Integration Breach Rewrites the Third-Party Risk Playbook
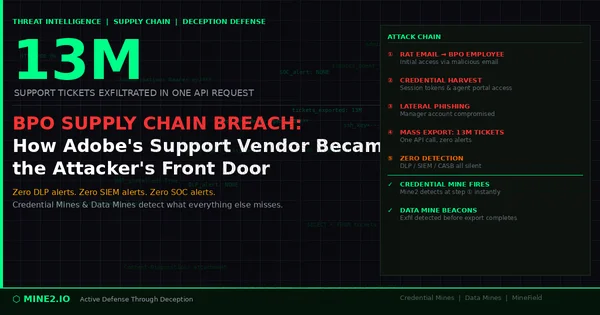
13 Million Tickets, One Request: How the Adobe BPO Breach Exposes the Third-Party Credential Blind Spot
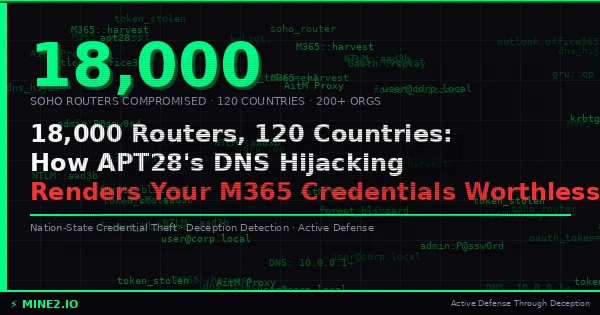
18,000 Routers, 120 Countries: How APT28's DNS Hijacking Campaign Renders Your M365 Credentials Worthless
Need Security Help?
Protect your organization with MINE2's cyber deception platform.